
Bitcoin is a new type of money that relies on computers around the world to mine new coins into existence, send & receive to wallets, and validate & verify transactions. Without computers and the internet, bitcoin wouldn’t be possible. But computers can be hacked – so can bitcoin be hacked too?
According to one of the top computer security researchers in the world, Dan Kaminsky, the answer is no, Bitcoin cannot be hacked.
With billions of dollars on the line, there is an active interest in hacking bitcoin. Anyone who could hack bitcoin would be instantly rich, insanely famous, or at the very least, have an intense pride in knowing that they finally figured out how to hack the unhackable.
There’s a good reason bitcoin hasn’t been hacked: bitcoin is a distributed network. There is no central bitcoin server. There is no company database. There is no person in charge.
There are many things in bitcoin which can be hacked (and have been hacked), but taking down a single node, or injecting malware into a single wallet software, or hacking a single exchange does not do any damage to the network itself aside from public reputation damage.
Can Bitcoin Be Hacked With Any One Of These Methods?
Bitcoin Network Hack
Most people who don’t trust Bitcoin because they think it can be “hacked” don’t really understand bitcoin. You can’t hack the bitcoin network because there’s no central thing to hack. You can disrupt part of bitcoin’s ecosystem, but there’s no central point of failure. Bitcoin was designed to function in an adversarial environment.
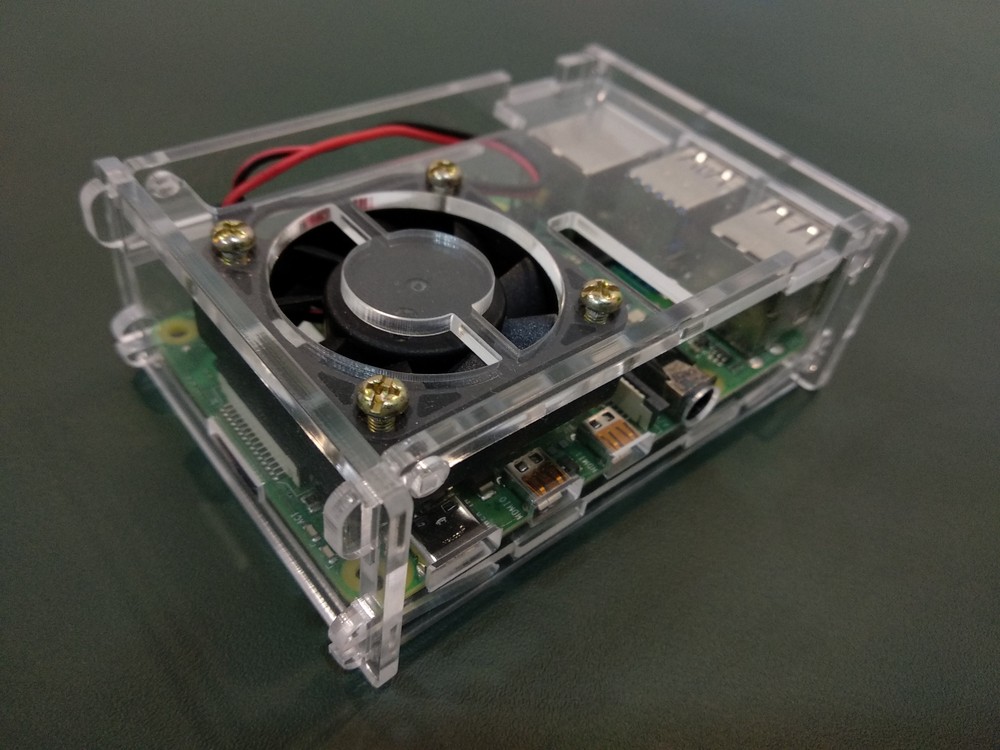
When someone mines bitcoin, they are not the only miner. There are thousands of miners around the world. When someone validates bitcoin transactions with a node, they are not the only validator. There are tens of thousands of validators in every country in the world, even in North Korea and Afghanistan. You can infect someone’s wallet, browser, or computer with malware, but you can’t hack the millions of bitcoin owners everywhere, all at the same time.
Anywhere there’s internet you can participate in the bitcoin network.
It’s not possible to hack the Bitcoin network because there’s nothing to hack.
That’s not to say that bitcoin doesn’t have vulnerabilities. There are many ways to lose your bitcoin though social engineering, software hacks, hardware hacks
Related Content
Bitcoin Software Hack
So, you can’t hack the network, but could you hack the bitcoin software? Would it be possible to distribute some kind of malware to the bitcoin software that’s running on bitcoin nodes, validating transactions? Maybe, but there would be some serious limitations to this kind of attack, and the results of such an attack would probably be short-lived.
To do such an attack, you’d have to first sneak your code into a bitcoin software update. But wait – there are multiple implementations of the bitcoin software, meaning you’d need to hack multiple types of software at the same time. OK, so maybe you decide to hack the most popular and widely used Bitcoin implementation, Bitcoin Core.
Hacking Bitcoin Core
To send out a Core update that contained malicious code, you’d first need commit access, which is limited to just a few people who are intimately familiar with the Bitcoin Core and are frequent contributors. To do this, you’d either need to run a years-long social engineering campaign to gain the trust of Core contributors, with only the possibility that you’d get commit access in the future, or you’d have to become such a proficient Bitcoin developer that you were able to create and campaign for an update that would fool the most proficient Bitcoin developers in the world.
Sure. Maybe. Except that Bitcoin is open source, meaning everyone in the world can see the code, so you’d also have to sneak your malware past the eyes of every single person in the world who has eyes on Bitcoin’s code.
Honestly, there are not that many people who are watching the code, and mistakes happen, so let’s say that hypothetically you get your hack under the hood and it launches.
Bitcoin Updates Are Not Automatic
Unless it’s a hard fork, which is highly unlikely at this point, users would NOT be required to upgrade, meaning there would not be a system-wide forced update. Users can update at their leisure since the code will be backward compatible, and some people may take years to do so. So, either your hack would affect only a small number of nodes that immediately update, or you’d have to sit and wait years to run your exploit scheme, and hope that nobody notices the malicious code in the meantime.
All of that is to say that if you “hacked the bitcoin software”, it wouldn’t affect the whole network at one moment, so the hack would not be catastrophic. It would require a series of increasingly unlikely events, and then, at the end of the day, what would you hope to achieve?
If your goal was to give yourself more coins, your hack would have just delegitimized the security of the Bitcoin network, so your coins would be worth way less now. Considering that in the process of trying to hack bitcoin you became the most proficient bitcoin developer in the world, you might as well just contribute to the project and earn some bitcoin for your skills.
More specifically though – what would a hack actually do? Remember the nodes only validate transactions, and you still have the miners in the network that are creating blocks and choosing which transactions to include. I’m not really sure what a hack of the node software would accomplish.
The Last Resort
If your goal was simply to cause chaos or destroy the network once and for all, in a worst case scenario situation, maybe you could secretly introduce some kind of Manchurian candidate type of bug into the software to be revealed decades later.
It could cause lots of chaos to the system, but bitcoiners still have one tool in their belt – a hard fork. This would be difficult to implement, and would certainly cause some problems, but it’s an option. It would kind of depend on how bad the hack was, and how urgent a fix was needed.
In the unlikely event that something like this happened, it’s an option to hard fork bitcoin to roll back the software to a previous update or to a new update that did not include the bug. Honestly, this would not be a simple thing to do, but it’s not like bitcoin would be dead forever.
Bitcoin Miner Hack
One of the more interesting ideas to consider is the possibility of wide-scale bitcoin miner vulnerability that could disrupt bitcoin mining in some way, compromising network security. While this is a possibility, it’s unlikely to affect the network as a whole and the possibility of it being a problem in the future decreases with time.
As far as I know, a mining “hack” has never occurred, but there were some events in the past which could be construed as the introduction of a mining vulnerability.
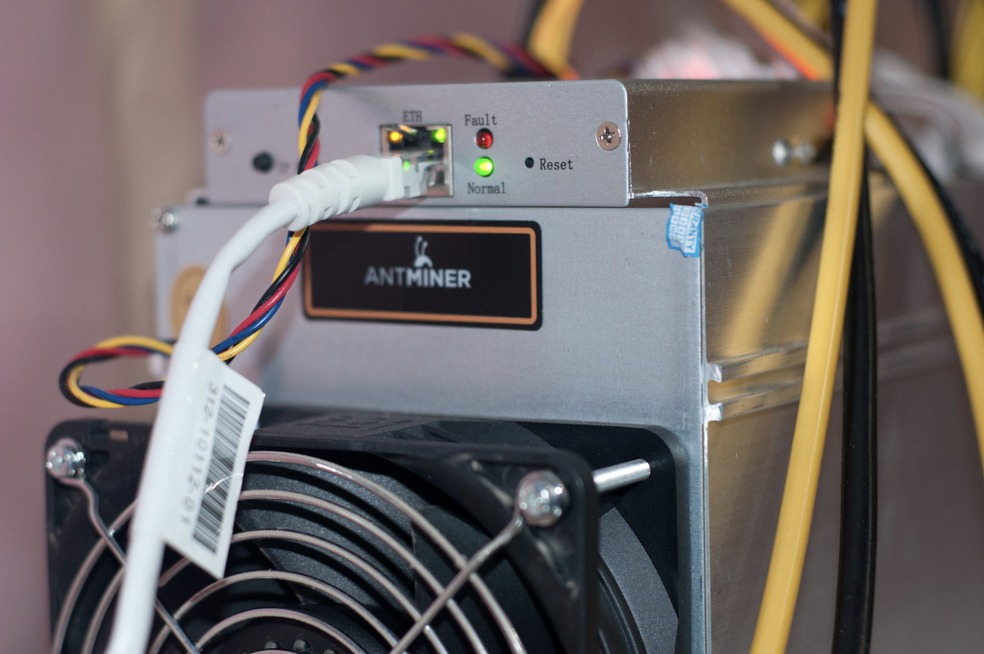
Antbleed
For example, in 2014, some bitcoin miners from one of the main bitcoin ASIC manufacturers were shipped with some dormant code that would allow them to be remotely turned off. This was called Antbleed, and sparked the creation of the open-source mining firmware Braiins. The manufacturers of the mining equipment said this was a feature, not a bug, which would allow miner owners to remotely shut down their own miners in the case of miner confiscation, which had been done several times in the past. However, the community interpreted it as Bitmain retaining the option to remotely shut down any miners they manufacture.
Regardless, if you’re running your own firmware, these days it’s not an issue.
Man In The Middle Attack
There’s another theoretical miner attack called a man in the middle attack, which means that some miners could be vulnerable to having their bitcoin rewards intercepted. The good news is that there’s already a fix for this, with a mining software update called Stratum V2, and this is not something that would affect the mining that occurs over the entire network. It would be a targeted attack on a single miner, which would only happen for a short period of time before being discovered.
What’s more, long-term network-wide mining vulnerabilities aren’t an issue. As bitcoin mining remains profitable for longer, the number of bitcoin miner manufacturers is likely to increase. For example, just in 2021/2022, there were major announcements regarding the future of bitcoin mining.
More Diverse Mining Hardware On The Horizon
First, Blockstream entered the mining space in a huge way in 2021. They acquired Spondoolies in an effort to start manufacturing their own Blockstream branded ASIC. Second, they started making portable solar mining rigs in shipping containers, and you can be sure that the technical wizards at Blockstream keep those containers secure.
Second, Block (formerly Square) made an announcement that they are building their own bitcoin miner as well. Though details are sparse at the moment, this is clearly an effort to make bitcoin mining hardware more accessible to the average user and more resilient as well. They are specifically working with the community to solve the problems of your average pleb bitcoin miner.
How YOUR Bitcoin Could Be Hacked
Computer Hack

If your computer is hacked, your bitcoin could be at risk. I’m using “hack” in a broad sense here because there’s a wide range of things that could compromise your computer’s security. You could actually be hacked, meaning that someone has full control of your machine, or you could just have some malware on your machine.
This is a local issue, not an issue with the Bitcoin network.
The main purpose of a computer hack would be to steal your private keys. This is why you should never write down your seed phrase into your computer. Ever. Don’t write it in a note pad. Don’t save it to your password protector. Don’t take a picture and store it in your iPhone. There are types of malware specifically designed to scan for this type of information.
Never Type Your Seed Phrase Into Your
All the best hardware wallets will never have you enter your keys using a keyboard to prevent a keylogger from tracking the keys as you type, and will generate your keys in a secure way that the computer cannot read.
If you want to take it a step even further, you can disconnect your machine from the internet as you generate your keys. Keys are generated on the device itself, so do not need an internet connection.
Browser Hack

Another way you could lose some bitcoin is through a browser hack. This is probably not likely related to the browser itself. Instead, it would be related to some kind of malicious browser extension or wallet you downloaded. I’ll discuss wallet hacks specifically below.
The main way a browser could steal your bitcoin would be to 1) intercept a bitcoin transfer and 2) steal your bitcoin private keys. Preventing this is pretty easy, but requires that you are always vigilant when interacting with your bitcoin wallet.
First, always double-check the bitcoin receive address on your hardware wallet. A malicious browser attachment could replace a receive address, causing you to send bitcoin to the wrong person. Bitcoin transactions are irreversible, so your coins would be lost.
Never Type Your Seed Phrase Into A Browser
Second, never type your seed phrase into a browser, even if your computer prompts you to do so. Fake notifications are easy to create and difficult to spot if done well.
Think of it as similar to email. If you receive a random email asking you to verify your bank account password, you should be suspicious. Go directly to the bank website and log in there, instead of via email link. You should be equally suspicious if your browser or wallet prompts you to enter your seed phrase. Most never will.
With a browser, basic security measures mean that you shouldn’t be downloading and installing random extensions then blindly following prompts that give them access to your computer. There have been many instances of malicious extensions in the past, and there will continue to be more in the future. This problem is not going away, and it’s not limited to Bitcoin.
Exchange Hack

Though not as frequent as in the early years of Bitcoin, exchange hacks are definitely something to be aware of and protect yourself from. That’s why it’s important to keep the bulk of your bitcoin savings off exchanges. If you are not intimately familiar with the security practices of the exchange you use, then you really have no idea how they are securing your bitcoin.
The Mt. Gox exchange was hacked in 2014, and people are still waiting on a lawsuit in Japan to complete so they can get a portion of their coins back. It’ll probably be 10 years total before they actually get their compensation, and in this case, they would be considered lucky. Sometimes, the coins are just gone and that’s the end of the story.
These days, security practices are much better, and to be honest, the Mt. Gox thing is so memorable because it was so catastrophic due to the irresponsibility of the exchange. For example, Crypto.com was hacked as recently as January 2022, but all affected customer funds were made whole by insurance.
What happens if they don’t have insurance? Or not enough insurance to cover your losses? Or it takes a while to recover the funds and you need the money in the meantime. Your exchange having insurance doesn’t guarantee that you’ll get the bitcoin you’re owed.
Account Hack

The most common way to lose bitcoin is, fortunately, very easy to prevent, which makes it the most unfortunate type of hack. Accounts hacks are common mostly because people are lazy. They used an insecure password, didn’t use 2-factor authentication, or didn’t set up address white listing, or implement other types of login verification methods available to them.
Most of all, however, it’s the user’s fault for keeping their bitcoins on an exchange.
Of course, account hacks suck, and it’s not always 100% the user’s fault. If their coins weren’t on an exchange, then they wouldn’t have this problem, but we all make mistakes. It’s human nature to take shortcuts, be lazy, hope for the best, and not expect the unexpected.
An account hack would mean that your personal account on a bitcoin exchange was compromised. The exchange itself was not hacked, so other users were not affected. Just your account.
The number 1 way to prevent a catastrophic event like this would be to keep your bitcoin off of exchanges. Withdraw your coins to your own hardware wallet and secure your private keys offline. At the very least, just keep a small portion of your stack on an exchange that you may need to sell for cash in an emergency.
Securing Your Accounts With 2FA
Outside of that, the best way to secure your account is to use 2-factor authentication (2FA) which is NOT SMS-based. Phone numbers can be spoofed, and emails can be hacked as well. 2FA through a local phone app like Authy or Google Authenticator or a hardware device like a Yubikey are the best methods. That means nobody can get into your account without having a physical, local device that you have. There’s no “password” they can use. They need the hardware that only you have.
The burden, then, is that you have one more thing to keep track of. It’s possible to recover keys with Authy, through a verification process. Google Authenticator gives you some physical backup codes you can store offline. I’m not sure if any exchanges actually use Yubikey as an option, but it might be smart to have two, and keep one handy, with the other one in a secure location.
Wallet Hack

Another possibility for losing your bitcoin is through a wallet hack. This is more common with software wallets than hardware wallets, but both are possible.
Software Wallet Hacks
There have been many types of bitcoin wallet vulnerabilities in the past, but none were due to problems with the bitcoin network itself. These were either due to user error, or insecurities within the bitcoin wallet itself.
For example, there was a popular website called Brain Wallet in the early days, which would create a bitcoin private key hash from any phrase you entered into the site. This meant you could use something memorable, like the first sentence of your favorite book.
However, it was discovered later that there are bots out there testing all types of text to find these types of wallets, and even obscure texts have been guessed, with bitcoin stolen from them. This was due to the lack of “randomness” (entropy) during seed generation.
In 2023 it was discovered that one of the most popular browser wallets, Trust Wallet, was not generating seeds properly and an incredible amount of user funds were at risk for a period of time. If your wallet isn’t generating seed phrases properly and you don’t have a passphrase (13th or 25th word), then your bitcoin could be hacked.
Hardware Wallet Hacks
With a hardware wallet, a “hack” isn’t really realistic, in that a hacker would not be able to reach into your hardware wallet and sweep your funds without your permission. The catch here is that if you are not aware you are giving them permission to take some funds, you could still lose your bitcoin.
The best example of this is the Ledger vulnerability (since patched) where an attacker could trick you into thinking you’re sending an altcoin, but you are really sending your bitcoin to an attacker’s address. This would require 1) you intend to spend an altcoin in the first place and 2) approve the transaction and the receive address. Always check the details before sending transactions!
In 2023, it was discovered that fake Trezor wallets were being sold. They looked exactly like the real thing, and could even generate a variety of seed combinations. However, hackers had already compromised all versions of possible seeds generated by this device, and eventually stole funds while the users funds were deep in cold storage.
Another crazy example of this was when the Ledger’s customer list was hacked, then users were sent fake hardware wallets in the mail, asking them to transfer funds to the “new and updated” device”
Even though there were warning signs in both of these situations situations, many of us get lazy or distracted, especially when transacting in bitcoin frequently. Many beginner users don’t know the difference.
About Seed Phrase Security
Though it’s not really possible to hack bitcoin, there are still plenty of ways to lose your bitcoin. Even if your devices and tools are not hacked, per se, the main way people lose their bitcoin is by not securing their bitcoin seed phrase properly. Bitcoin is stored in the bitcoin ledger, and your seed phrase is the key to unlock and spend your bitcoin.
Nobody really owns bitcoin, we just look after the keys for the next generation
Bitcoin Axiom
That means if someone gets a hold of these keys, they can spend your bitcoin. If you lose these keys, there’s no way to recover them. It’s very important that you keep your bitcoin keys secure!

These days, there are way more options for storing private keys thanks to BIP-39. Instead of a long string of random letters and numbers on a paper printout, you can now choose to store your 12- or 24-word seed phrase in a variety of secure methods. With the introduction of multisignature schemes in 2012 and newer tools like SeedXOR and Shamir Secret backups, the options and quality of bitcoin private key security is getting better all the time.
My favorite options are the ones that help prevent you from shooting yourself in the foot!
Phishing & Social Engineering
The easiest way for an attacker to get you to give up your bitcoin is to have you (unknowingly) volunteer to do it. They can do this with a wide range of tactics, but they all center around the idea of getting you to type your seed phrase into your computer. For the vast majority of newbies, most of the time, you’ll never need to do that.
One common scam that goes around is by getting users to download fake updates to desktop wallets. The malware will either sweep funds from hot wallets that contain bitcoin or ask you to update your wallet and type in your seed phrase to complete the update.
This is one reason why I prefer to use a hardware wallet, and I do not keep any significant amount of funds on desktop or mobile hot wallets.
These types of phishing schemes are not limited to wallets. Websites, browsers, and emails can also trick you into giving up your seed phrase. They may use a “carrot” or a “stick” method to do it. For example, they could claim that you can redeem extra bitcoin by “verifying” your holdings, like a giveaway scam. That would be the carrot, enticing you with the promise of free money.
You may also see fake warnings about hacks or other security problems, claiming that your wallet was hacked and you need to update it, or that bitcoin is at risk. That would be the stick, making you fear that your bitcoin is at risk.
Social Engineering
In terms of social engineering, there have been several instances of young men getting courted by women, then drugged or beaten into giving up their bitcoin. The authenticity of some of these events has been disputed in some cases, but the risk is still there. If you brag about your holdings and keep your funds on a hot wallet, or even an easily accessible cold wallet, then you could be at risk for this type of social engineering attack.
In this case, the best opsec is simply to be humble and don’t advertise how much bitcoin you have, as tempting as it can be if you meet your goals and have a nice stack going on.
The specifics of these attacks will change over time, so when you think about security, think broadly, and think long term. For example, a rule of thumb is to never type your seed phrase into a keyboard. Simple. I also like to keep my bitcoin so it’s not immediately accessible to me, and I never reveal how much I have. Simple.
You can also set up your private key security so it’s fool-proof with something like a custodial multisig.
Partial Seed Phrases Are NOT Secure
The saying in Bitcoin Land goes DYOR (Do Your Own Research). There’s lots of advice online, and not all of it is good. One of the most disappointing things to read online is that you should “split” your seed phrase and separate the parts to make it more secure. This is bad advice.
If you have a 12-word seed phrase, do not split it into two parts, then give 6 words to your dad and 6 words to your mom. You screw yourself in two ways.
- You can’t personally recover your own phrase without the two parts
- If someone discovers just one part, they can brute force the rest
You’ve not only shot yourself in the foot, but you’ve also given someone else a gun to shoot you in the other foot.
If you want to add some extra security to your bitcoin wallet, you can use what’s called a “passphrase”, or a 25th word. Your normal private key remains intact, but you add an “additional secret wallet” behind this 25th word. It can be a single word (insecure) or a sentence (more secure). Since this phrase is not part of the BIP-39 2048 word list, it’s impossible for anyone to guess without brute forcing it, and the longer your passphrase, the harder it is to hack.
As a side benefit, it also gives you plausible deniability to any attacker, as they can’t know for sure if you have any funds in a secret wallet, so you can put some decoy funds in your basic wallet, with the majority of your funds hidden.
Multisig
Another great option used by a lot of bitcoiners is “multisig”, meaning that you have multiple signing devices secure your bitcoin, so there is no single point of failure. With a single key, if you lose your device or your seed phrase, your bitcoin is gone forever. With a 2-of-3 multisig, you need just two of the three devices to sign for a transaction, and can restore your wallet even if one of the three devices or keys is compromised.
You can easily set up your own multisig scheme using Sparrow Wallet, Specter Wallet, Lily Wallet, or you can do it as part of a partial-custodial scheme with Unchained or CASA.
Most people who do multisig also geographically distribute their keys, so you can keep one key at home, and two at other locations. Popular locations could be a place of work, a bank safe deposit box, or at a trusted family member’s house.
In my opinion, even if all devices and seeds are at one very secure location, although that place is a single point of failure, you still have the added protection of multiple devices, in case of hardware failure. At the same time, however, it may introduce complexity to your bitcoin recovery process, and complexity is a good way to footgun yourself.
Shamir Secret Backup
Another option is called a Shamir Secret Backup, in which you have a single signing device with a single key, but that key is then split into “shards” which act like a multisig of your single key. This means you can move your funds with a single device, but to back up your device, you’ll need enough of the shards to recover the funds. Again, this is not simply splitting your 12-word phrase into three separate 4-word pieces. There will be a unique 12 or 24-word set of words for each shard, so a 2-of-3 Shamir Secret scheme could possibly have three sets of 24 words.
Seed XOR
Yet another interesting tool is called Seed XOR, which means that several “decoy” backup keys are created with the same signing device and seed phrase. These are not “new” keys. They are sets of backup words derived from your original seed. You don’t need multiple sets of words for recovery in this case, but you could. In this case, instead of requiring two of three, you’d need three of three, and each of the three seeds could also act as their own individual wallet.
Passphrase
Perhaps the simplest to understand and implement however, is going back to the passphrase option previously mentioned. It’s simple to implement and understand
- Buy a hardware wallet
- Store your seed in steel (then hide)
- Add a passphrase for a secret wallet
This is probably the best strategy for newbies, then you can play around with the others as you have time and get more paranoid about protecting your bitcoin stack.
Frequently Asked Questions
What Are The Odds Of Guessing A Seed Phrase?
With 2048 words combine in 12-word combinations, there are as many possible bitcoin seed phrases as there are grains of sand in 1000×1000 Earths. The possibility of guessing a seed phrase is the same possibility of guessing a single grain of sand in over a million Earths.
What To Do If Your Seed Phrase Is Compromised?
If your seed phrase has been compromised, either partial or whole, you should transfer your bitcoin to a newly generated wallet with an entirely new seed phrase. If you want to use the same hardware wallet, you’ll need to send your funds to a temporary wallet, reset your hardware wallet to generate a new phrase, then send the funds back to the new phrase.
Do Bitcoin Wallets Always Have Seed Phrases?
Not all bitcoin wallets have seed phrases! Some bitcoin wallets are lightning wallets by default, therefore custodial wallets. This means that a company is holding custody of your funds. Although these funds are legally yours, the wallet could hypothetically steal your funds, authorities could confiscate them, or a hacker could compromise the wallet and take your funds.
How Likely Is Bitcoin To Be Hacked?
Bitcoin is very unlikely to be hacked. After 14 years in existence, holding 500 billion dollars in wealth, and transferring billions of dollars in value daily, if it was going to be hacked, it would have happened already.
Can Someone Hack My Bitcoin With My Wallet Address?
No one hack your bitcoin wallet by knowing your bitcoin “address”. Actually, your bitcoin wallet should generate a new bitcoin address every time you receive funds. Even if it does not, however, your public receive address is public for a reason – you need to receive funds! It’s derived from your private key, which will then allow you to spend the bitcoin, but there is no way for the sender to figure out your private key simply from knowing your receive address or even your xPub (extended public key)















 Can You Lose Money In Bitcoin?
Can You Lose Money In Bitcoin?
Leave a Reply